Key Takeaways:
- Measuring cybersecurity maturity gives leadership visibility into performance, gaps, and ROI — beyond basic compliance reporting.
- Aligning security programs to frameworks like NIST CSF helps teams prioritize controls that reflect operational risk.
- Building measurable cybersecurity programs requires clear metrics, cross-environment visibility, and reporting that translates technical performance into actionable business insights.
—
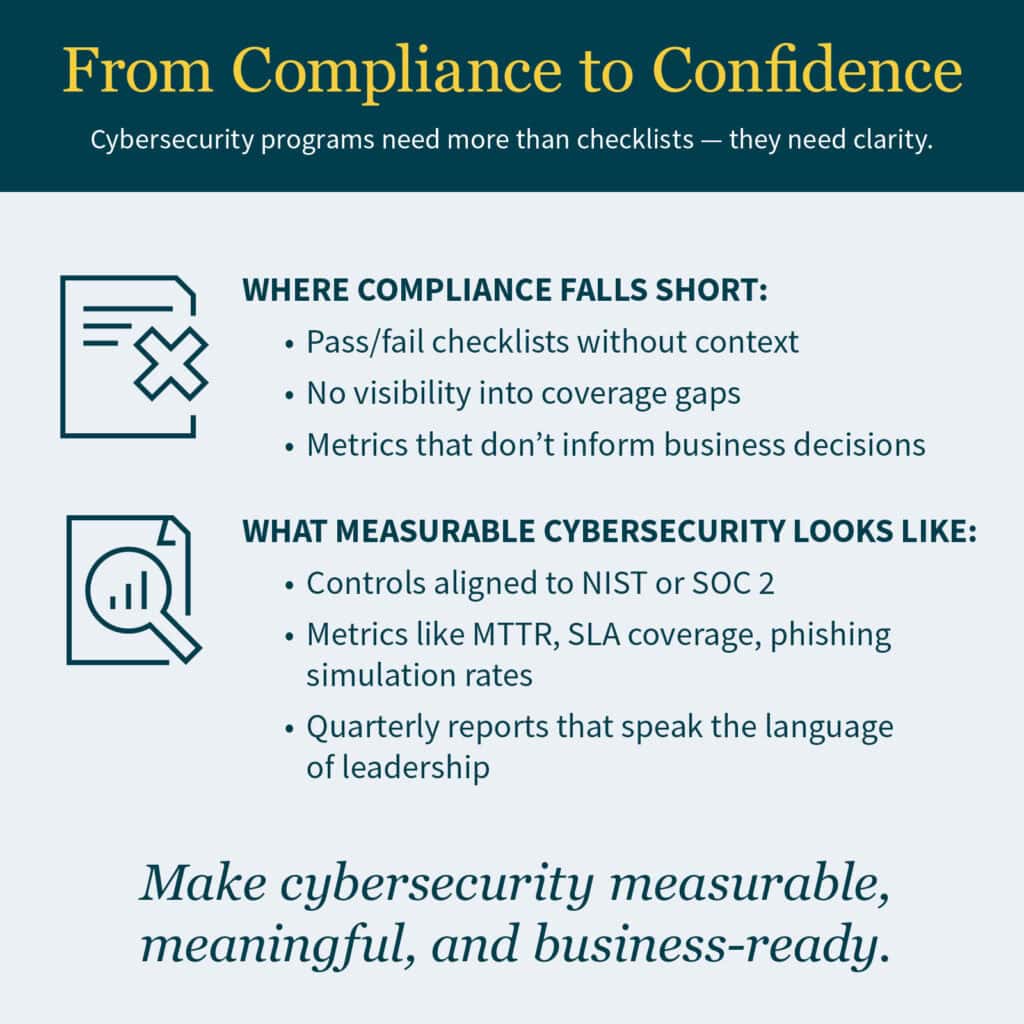
Most organizations understand the need for cybersecurity — but fewer know how to measure its effectiveness. For middle-market companies and resource-constrained teams, it’s often easier to focus on passing audits than building long-term resilience.
Compliance alone doesn’t guarantee protection. As threats evolve and executive teams demand more transparency, cybersecurity programs must move beyond checklists to deliver measurable value. Leaders want to know:
- Are we truly protected?
- Where are the gaps in our defenses?
- What return are we getting on our investments?
This shift — from compliance to confidence — starts by making cybersecurity measurable in practical, business-relevant ways. By aligning metrics with risk reduction, operational performance, and strategic goals, organizations can demonstrate progress, justify investments, and build trust at every level.
Why Compliance Alone Falls Short
Passing an audit doesn’t always mean you’re secure. Many compliance frameworks are backward-looking, designed to validate past controls rather than assess real-time risk. As a result, they can overlook emerging threats and gaps in coverage that attackers exploit today.
According to the State of Cybersecurity 2025 report, over half of respondents say they struggle to measure cybersecurity performance. Some of the most common challenges include:
- Limited visibility into tools, endpoints, and cloud assets
- No standardized metrics for incident response or threat detection
- Difficulty translating technical controls into board-ready insights
- Reactive investments driven by fear or regulation, not strategy
Organizations that rely only on “pass/fail” compliance indicators often miss opportunities to strengthen their environment — and struggle to justify budget over time. True resilience requires going beyond compliance—integrating continuous monitoring, proactive risk assessments, and adaptive security measures that evolve with your environment.
A maturity-based approach provides a clearer path to improvement and better alignment with risk.
Industry Spotlight: Financial Services
In financial services, compliance is essential — but not enough. Boards and regulators increasingly expect proof that security controls are actively reducing risk, not just fulfilling annual audit requirements.
To meet these expectations, financial institutions can adopt a maturity model aligned with frameworks such as the National Institute of Standards and Technology (NIST) Cybersecurity Framework (CSF) or Federal Financial Institutions Examination Council (FFIEC). This approach enables organizations to:
- Measure and track control strength over time
- Benchmark performance against industry standards and peers
- Demonstrate how security investments translate into reduced risk exposure
A metric-driven strategy transforms compliance from a checkbox exercise into a proactive risk management program — building trust with stakeholders and strengthening resilience in a fast-moving threat landscape.
What It Means to Be “Mature” in Cybersecurity
A “mature” cybersecurity program isn’t perfect — but it is proactive, risk-aligned, and measurable. Rather than reacting to threats or relying solely on compliance, mature programs embed security into business strategy and decision-making.
Key characteristics include:
- Visibility: You know what systems, users, and data are in scope — and what’s protected.
- Prioritization: Controls are applied based on risk level, not only compliance requirements.
- Measurement: There are clear, repeatable metrics for program performance.
- Accountability: Leadership has insight into progress, gaps, and investment needs.
This approach elevates cybersecurity from a technical function to a strategic enabler, improving decision-making at all levels — from the security operations center (SOC) to the C-suite.
Steps to Make Cybersecurity Measurable
Here are practical, actionable steps your team can take today to turn cybersecurity into a measurable, business-aligned program:
1. Start With a Framework-Based Controls Review
Choosing a structured framework gives your team a foundation for measuring progress.
Frameworks like NIST CSF, Health Insurance Portability and Accountability Act (HIPAA), or SOC 2 provide a roadmap that helps you:
- Identify existing strengths and gaps in security posture
- Group controls by function (identify, protect, detect, respond, recover)
- Establish a common language across departments
- Benchmark your program against industry norms
A formal controls review helps organizations understand not just where they stand today — but what’s next. By aligning security efforts to a recognized framework, organizations can set measurable goals, track progress over time, and demonstrate value to stakeholders.
2. Define Key Metrics That Matter
Once your baseline is clear, the next step is to build out practical key performance and risk indicators (KPIs and KRIs) that reflect real-world security state. These metrics should be actionable, measurable, and aligned with business objectives — not just technical outputs.
Examples include:
- Number of incidents detected and contained within service level agreement (SLA)
- Percentage of critical assets covered by monitoring
- Phishing simulation pass rates
- Mean time to detect (MTTD) and mean time to respond (MTTR)
- Also: MTTD vs MTTR, mean time to conclusion (MTTC), mean time to failure (MTTF), mean time between failures (MTBF)
- Audit readiness score by business unit
Avoid the trap of over-measuring. Focus on 5–7 metrics that map directly to risk reduction and show improvement over time.
3. Improve Visibility Across the Environment
You can’t measure what you can’t see. Yet many teams work without complete visibility across cloud, on-premises, and third-party environments — creating blind spots that attackers exploit.
As part of a security architecture and controls review, organizations can assess visibility across cloud, on-prem, and hybrid environments to:
- Find unmanaged assets and unknown endpoints
- Uncover gaps between departments or systems
- Strengthen monitoring where risk is highest
Better visibility leads to more correct metrics and faster response times.
4. Build Reporting for Decision-Makers
Cybersecurity reporting shouldn’t stay confined in the SOC. Mature programs translate technical data into insights for executives, boards, and external stakeholders, bridging the gap between security operations and business strategy.
Effective reporting can include:
- Quarterly maturity scorecards
- Visual dashboards tracking core metrics
- Narrative summaries with business impact context
- Audit preparation reports aligned to frameworks and risk areas
When security performance is visible and tied to business outcomes, leaders are more likely to fund, support, and champion the program.
Building a More Accountable Cyber Program: How MGO Helps
At MGO, we help organizations strengthen their cybersecurity posture by identifying key risks, refining policies, and aligning security practices with compliance and operational goals.
Our team supports clients across industries — including life sciences, cannabis, manufacturing, and state and local government — with guidance rooted in experience, not hype.